Ejbca Generate Ecdsa Public Key
| Developer(s) | PrimeKey Solutions AB |
|---|---|
| Initial release | December 5, 2001 |
| Stable release | 7.3.1.2 / March 23, 2020 |
| Repository | |
| Written in | Java on Java EE |
| Operating system | Cross-platform |
| Available in | Bosnian, Chinese, Czech, English, French, German, Japanese, Portuguese, Swedish, Ukrainian, Vietnamese |
| Type | PKI Software |
| License | LGPL-2.1-or-later |
| Website | www.ejbca.org |
EJBCA, is a free softwarepublic key infrastructure (PKI) certificate authority software package maintained and sponsored by the Swedishfor-profit company PrimeKey Solutions AB, which holds the copyright to most of the codebase. The project's source code is available under terms of the Lesser GNU General Public License.
Design[edit]
The system is implemented in Java EE and designed to be platform independent and fully clusterable,[1] to permit a greater degree of scalability than is typical of similar software packages. Multiple instances of EJBCA are run simultaneously, sharing a database containing the current certificate authorities (CAs). This permits each instance of the software to access any CA. The software also supports the use of a hardware security module (HSM), which provides additional security. Larger-scale installations would use multiple instances of EJBCA running on a cluster, a fully distributed database on a separate cluster and a third cluster with HSMs keeping the different CA keys.
Ecdsa - Create Private key and Bitcoin Address. How to generate a public key from a private key using Elliptic Curve Digital Signature Algorithm. EJBCA Enterprise and Public Key Infrastructure (PKI) As the world’s most used PKI (Public Key Infrastructure), certificate issuing and management software, EJBCA Enterprise provides you with the basic security services for trusted identities and secure communication in any environment and use case. I am trying to generate implicit ECDSA certificate only for signing and verification using OpenSSL. I tried google but I am getting many research papers. I understood that A messages need to be signed using ECDSA over the NISTp256 curve with ECQV certificates. I couldn't figure-out how. How to generate a public key from a private key using Elliptic Curve Digital Signature Algorithm. Andreas says a point in an elliptic curves can be added to itself by drawing a tangent, finding the intersection, then reflecting the new point on the x-axis.
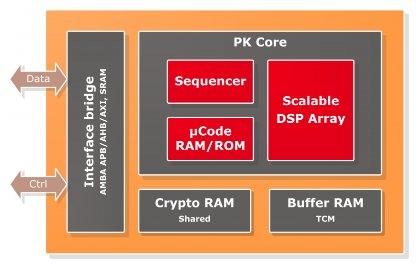
EJBCA supports many common PKI architectures[2] such as all in a single server, distributed RAs and external validation authority. An example architecture is illustrated below.
Key features[edit]
- Please delete colons ':' and new lines for the private key and the public key and fill 'EC private key (hex)' and 'EC public key (hex)' in above form and choose proper curve name, then you can use them for signing and verification.
- Public / Private Keys and Signing. In blockchain, the signature algorithm is the Elliptic Curve Digital Signature Algorithm or ECDSA (https. Create a public/private key pair; to generate the public key from the private key we use the secp256k1 algorithm from before.
Multiple CA instances[edit]
EJBCA supports running unlimited number of CAs and levels of CAs in a single installation. Build a complete infrastructure, or several, within one instance of EJBCA.
Online Certificate Status Protocol[edit]
For certificate validation you have the choice of using X.509 CRLs and OCSP (RFC6960).
Registration authority[edit]
The EJBCA software includes a separate registration authority (RA) front end that can run on the same instance as the CA or distributed as external RAs. Communication between the CA and the RA is only using outgoing network connections to insulate the CA from less trusted networks, where the RA is typically placed.
Multiple algorithms[edit]
You can use all common, and some uncommon algorithms in your PKI. RSA, ECDSA and DSA, SHA-1 and SHA-2. Compliant with NSA Suite B Cryptography.
Different certificate formats[edit]
EJBCA support both X.509v3 certificates and Card Verifiable certificates (CVC BSI TR-03110). Certificates are compliant with all standards such as RFC5280, CA/Browser Forum, eIDAS, ICAO 9303, EAC 2.10 and ISO 18013 Amendment 2 eDL.
PKCS#11 HSMs[edit]
Using the standard PKCS 11 API you can use most PKCS#11 compliant HSMs to protect the CAs’ and OCSP responders’ private keys.
Many integration protocols and APIs[edit]
EJBCA was designed with integration in mind. Most standard protocols are supported, CMP, SCEP, EST, and ACME as well as web services. Using integration APIs it is possible to integrate EJBCA as a certificate factory, not exposing its native user interfaces.
High performance and capacity[edit]
You can build a PKI with capacity of issuing billions of certificates at a rate of several hundreds per second.
References[edit]
- ^'Automated and large scale operations'.
- ^'PKI Architectures'.
Further reading[edit]
- Research and application of EJBCA based on J2EE; Liyi Zhang, Qihua Liu and Min Xu; IFIP International Federation for Information Processing Volume 251/2008; ISBN978-0-387-75465-9
- Chapter 'Securing Connections and Remote Administration' in Hardening Linux; James Turnbull; ISBN978-1-59059-444-5
- Exception-Handling Bugs in Java and a Language Extension to Avoid Them; Westley Weimer; Advanced Topics in Exception Handling Techniques Volume 4119/2006; ISBN978-3-540-37443-5
- A workflow based architecture for Public Key Infrastructure; Johan Eklund; TRITA-CSC-E 2010:047
- Secret Sharing Framework Based on Digital Certificates; Paul Crocker and Adolfo Peixinho; Proceedings of the 13th European Conference on Cyber Warfare and Security ECCWS-2014; ISBN1910309249
- Building and Managing a PKI Solution for Small and Medium Size Business; Wylie Shanks; SANS Institute InfoSec Reading Room; December 2013
- Post-quantum algorithms for digital signing in Public Key Infrastructures; Mikael Sjöberb; Degree Project in Computer Science and Engineering at KTH, Stockholm, Sweden 2017
External links[edit]
- Official website
Definition
Creates a new instance of an implementation of the Elliptic Curve Digital Signature Algorithm (ECDSA).
Overloads
| Create() | Creates a new instance of the default implementation of the Elliptic Curve Digital Signature Algorithm (ECDSA). |
| Create(ECCurve) | Creates a new instance of the default implementation of the Elliptic Curve Digital Signature Algorithm (ECDSA) with a newly generated key over the specified curve. |
| Create(ECParameters) | Creates a new instance of the default implementation of the Elliptic Curve Digital Signature Algorithm (ECDSA) using the specified parameters as the key. /net-protector-2013-key-generator.html. |
| Create(String) | Creates a new instance of the specified implementation of the Elliptic Curve Digital Signature Algorithm (ECDSA). |
Creates a new instance of the default implementation of the Elliptic Curve Digital Signature Algorithm (ECDSA).
Returns
A new instance of the default implementation (ECDsaCng) of this class.
Creates a new instance of the default implementation of the Elliptic Curve Digital Signature Algorithm (ECDSA) with a newly generated key over the specified curve.
Parameters
Returns

A new instance of the default implementation (ECDsaCng) of this class.
See also
Creates a new instance of the default implementation of the Elliptic Curve Digital Signature Algorithm (ECDSA) using the specified parameters as the key.
Parameters
- parameters
- ECParameters
The parameters representing the key to use.
Returns
A new instance of the default implementation (ECDsaCng) of this class.
See also
Creates a new instance of the specified implementation of the Elliptic Curve Digital Signature Algorithm (ECDSA).
Parameters
- algorithm
- String
The name of an ECDSA implementation. The following strings all refer to the same implementation, which is the only implementation currently supported in the .NET Framework:
'ECDsa'
'ECDsaCng'
'System.Security.Cryptography.ECDsaCng'
You can also provide the name of a custom ECDSA implementation.
Returns
A new instance of the specified implementation of this class. Office 2010 product key online generator. If the specified algorithm name does not map to an ECDSA implementation, this method returns null.
Exceptions
The algorithm parameter is null.
Remarks
If you develop your own implementation of an ECDsa object, you can use the Create(String) method overload to create a custom algorithm string that specifies your implementation.
Ejbca Generate Ecdsa Public Key Largo
If you specify a custom value for the algorithm parameter, the CryptoConfig object will use it to determine whether an ECDSA object can be created.